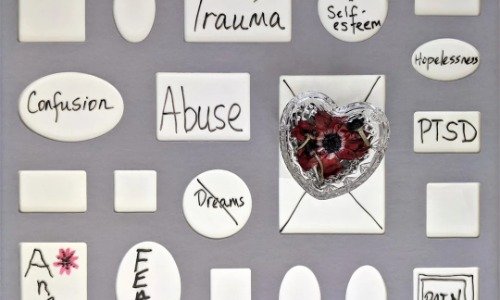
Worth Reading – Workplace Abuse, PTSD and Employer Duty of Care
Employees dealing with trauma outside of work often carry that trauma with them into work, and we need resources to help them navigate that. What do we offer people experiencing trauma at work who carry that trauma into the rest of their lives?
Maybe the better question is, what do we owe them?